Security Engineering on AWS (SISECO)

The Security Engineering on AWS (SISECO) Course is designed for participants who want to gain an in-depth understanding of Amazon Web Services (AWS) security technologies and best practices for managing security in a cloud environment. During the course, participants will learn how to secure applications and data in AWS, manage access to resources, implement advanced security techniques, and troubleshoot security issues. Additionally, they will learn how to meet security and compliance requirements by implementing appropriate security measures and managing security governance. The course helps prepare you for the AWS Certified Security – Specialty certification .
Course Objectives
Below is a summary of the main objectives of the Security Engineering on AWS (SISECO) course :
- Gain a thorough understanding of Amazon Web Services (AWS) security technologies.
- Learn to protect your applications and data on AWS through advanced security strategies and technologies.
- Manage access to AWS resources, ensuring that only authorized users can access relevant information and services.
- Implement advanced security techniques and resolve security issues in your AWS environment.
- Meet security and compliance requirements by implementing appropriate security measures and managing security governance.
- Master AWS Identity and Access Management (IAM) for secure user and permission management.
- Utilize AWS security tools like AWS Shield and AWS WAF for threat protection.
- Employ AWS CloudTrail and AWS Config for auditing and compliance monitoring.
Course Certification
This course helps you prepare to take the:
AWS Certified Security – Specialty exam ;
Course Outline
Module 1: Security on AWS
- Explain Security in the AWS cloud
- Explain AWS Shared Responsibility Model
- Summarize IAM, Data Protection and Threat Detection and Response
- State the different ways to interact with AWS using the console, CLI and SDKs
- Describe how to use MFA for extra protection
- State how to protect the root user account and access keys
Module 2: Security Entry Points on AWS
- Describe how to use multi-factor authentication (MFA) for extra protection
- Describe how to protect the root user account and access keys
- Describe IAM policies,roles,policy components and permission boundaries
- Explain how API requests can be logged and viewed using AWS CloudTrail and how to view and analyze access history
- Lab 1:Using Identity and Resource Based Policies
Module 3:Account Management and Provisioning on AWS
- Explain how to manage multiple AWS accounts using AWS Organizations and AWS Control Tower
- Explain how to implement multi-account environments with AWS Control Tower
- Demonstrate the ability to use identity providers and brokers to acquire access to AWS services
- Explain the use of AWS IAM Identity Center ( successor to AWS Single Sign-On) and AWS Directory Service
- Demonstrate the ability to manage domain user access with Directory Service and IAM Identity Center
- Lab 2: Managing Domain User Access with AWS Directory Service
Module 4: Secrets Management on AWS
- Describe and list the features of AWS KMS, CloudHSM, AWS Certificate Manager (ACM) and AWS Secrets Manager
- Demonstrate how to create a multi-Region AWS KMS key
- Demonstrate how to encrypt a Secrets Manager secret with an AWS KMS key
- Demonstrate how to use an encrypted secret to connect to an Amazon Relational Database Service ( Amazon RDS) database in multiple AWS regions
- Lab 3: Using AWS KMS to Encrypt Secrets in Secrets Manager
Module 5: Data Security
- Monitor data for sensitive information with Amazon Macie
- Describe how to protect data at rest through encryption and access controls
- Identify AWS services used to replicate data for protection
- Determine how to protect data after it has been archived
- Lab 4: Data Security in Amazon S3
Module 6: Infrastructure Edge Protection
- Describe the AWS features used to build secure infrastructure
- Describe the AWS services used to create resiliency during an attack
- Identify the AWS services used to protect workloads from external threats
- Compare the features of AWS Shield and AWS Shield Advanced
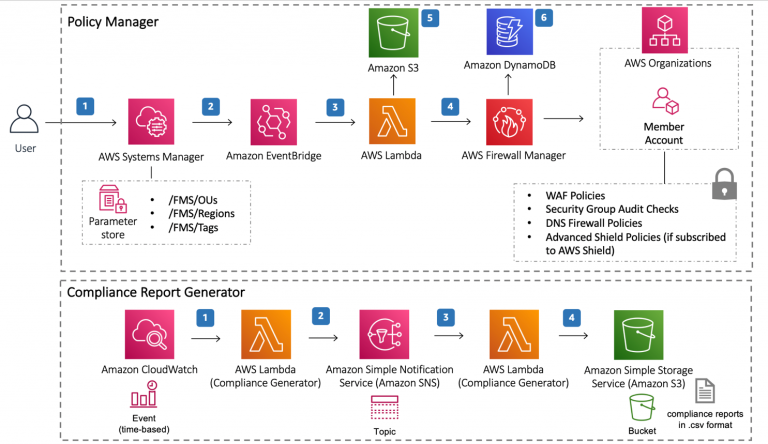
- Explain how centralized deployment for AWS Firewall Manager can enhance security
- Lab 5: Using AWS WAF to Mitigate Malicious Traffic
Module 7: Monitoring and Collecting Logs on AWS
- Identify the value of generating and collecting logs
- Use Amazon Virtual Private Cloud ( Amazon VPC) Flow Logs to monitor for security events
- Explain how to monitor for baseline deviations
- Describe Amazon EventBridge events
- Describe Amazon CloudWatch metrics and alarms
- List log analysis options and available techniques
- Identify use cases for using virtual private cloud (VPC) Traffic Mirroring
- Lab 6: Monitoring for and Responding to Security Incidents
Module 8: Responding to Threats
- Classify incident types in incident response
- Understand incident response workflows
- Discover sources of information for incident response using AWS services
- Understand how to prepare for incidents
- Detect threats using AWS services
- Analyze and respond to security findings
- Lab 7: Incident Response
Course Mode
Instructor-Led Remote Live Classroom Training;
Trainers
Trainers are Amazon AWS accredited instructors and certified in other IT technologies, with years of practical experience in the sector and in training.
Lab Topology
For all types of delivery, the participant can access the equipment and actual systems in our laboratories or directly in international data centers remotely, 24/7. Each participant has access to implement various configurations, Thus immediately applying the theory learned. Below are some scenarios drawn from laboratory activities.
Course Details
Course Prerequisites
- We recommend participation in the AWS Security Essentials Course and the Architecting on AWS Course .
Course Duration
Intensive duration 3 days;
Course Frequency
Course Duration: 3 days (9.00 to 17.00) - Ask for other types of attendance.
Course Date
- Security Engineering on AWS (Intensive Formula) – On request – 09:00 – 17:00
Steps to Enroll
Registration takes place by asking to be contacted from the following link, or by contacting the office at the international number +355 45 301 313 or by sending a request to the email info@hadartraining.com

