Microsoft Cybersecurity Architect SC-100

The SC-100 Microsoft Cybersecurity Architect Course is an advanced training program designed for participants who aim to become experts in designing and implementing cybersecurity solutions within the Microsoft ecosystem. This course offers participants a unique opportunity to deepen their knowledge and expertise in the field of cybersecurity, focusing on topics such as information protection, identity and access management, threat prevention, and regulatory compliance. During the course, participants will explore the various solutions and services offered by Microsoft to ensure the security of information, devices, and corporate infrastructure. Topics include designing and implementing security strategies, using cloud-based solutions such as Microsoft Azure and Microsoft 365, and integrating different technologies to ensure a holistic approach to cybersecurity. The course contributes to the preparation of the Microsoft Cybersecurity Architect Expert Certification exam .
Course Objectives
Here is a revised version of the objectives of the Microsoft Cybersecurity Architect SC-100 Course :
- Deep dive into security strategies in cloud and hybrid environments.
- Implement and manage advanced security solutions on Microsoft Azure.
- Designing robust security architectures, integrating Microsoft 365.
- Analysis and mitigation of vulnerabilities and cyber threats.
- Using Microsoft Technologies to Strengthen End-to-End Security
- Develop strategies for security governance and compliance management.
- Implement identity and access management solutions for enhanced security.
- Monitor and respond to security incidents and breaches effectively.
Course Certification
This course helps you prepare to take the:
Exam SC-100 Microsoft Cybersecurity Architect;
Course Outline
Design a resiliency strategy for ransomware and other attacks based on Microsoft Security Best Practices
- Design a security strategy to support business resiliency goals, including identifying and prioritizing threats to business-critical assets
- Design solutions that align with Microsoft ransomware best practices, including backup, restore, and privileged access
- Design configurations for secure backup and restore by using Azure Backup for hybrid and multicloud environments
- Design solutions for security updates
Design solutions that align with the Microsoft Cybersecurity Reference Architectures (MCRA) and Microsoft cloud security benchmark (MCSB)
- Design solutions that align with best practices for cybersecurity capabilities and controls
- Design solutions that align with best practices for protecting against insider and external attacks
- Design solutions that align with best practices for Zero Trust security, including the Zero Trust Rapid Modernization Plan (RaMP)
Design solutions that align with the Microsoft Cloud Adoption Framework for Azure and the Microsoft Azure Well-Architected Framework
- Design a new or evaluate an existing strategy for security and governance based on the Microsoft Cloud Adoption Framework (CAF) for Azure and the Microsoft Azure Well-Architected Framework
- Recommend solutions for security and governance based on the Microsoft Cloud Adoption Framework for Azure and the Microsoft Azure Well-Architected Framework
- Design solutions for implementing and governing security by using Azure landing zones
- Design a DevSecOps process
Design solutions for security operations
- Develop security operations capabilities to support a hybrid or multicloud environment
- Design a solution for centralized logging and auditing
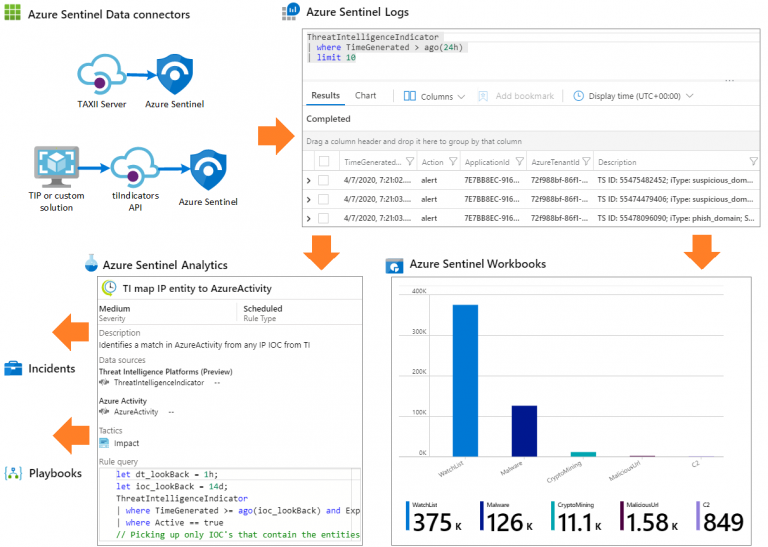
- Design a solution for security information and event management (SIEM), including Microsoft Sentinel
- Design a solution for detection and response that includes extended detection and response (XDR)
- Design a solution for security orchestration automated response (SOAR), including Microsoft Sentinel and Microsoft Defender
- Design and evaluate security workflows, including incident response, threat hunting, incident management, and threat intelligence
- Design and evaluate threat detection coverage by using MITRE ATT&CK
Design solutions for identity and access management
- Design a solution for access to software as a service (SaaS), platform as a service (PaaS), infrastructure as a service (IaaS), hybrid/on-premises, and multicloud resources, including identity, networking, and application controls
- Design a solution for Microsoft Entra ID, including hybrid and multi-cloud environments
- Design a solution for external identities, including business-to-business (B2B), business-to-customer (B2C), and decentralized identity
- Design a modern authentication and authorization strategy, including Conditional Access, continuous access evaluation, threat intelligence integration, and risk scoring
- Validate the alignment of Conditional Access policies with a Zero Trust strategy
- Specify requirements to secure Active Directory Domain Services (AD DS)
- Design a solution to manage secrets, keys, and certificates
Design solutions for securing privileged access
- Design a solution for assigning and delegating privileged roles by using the enterprise access model
- Design an identity governance solution, including Microsoft Entra Privileged Identity Management (PIM), privileged access management, entitlement management, and access reviews
- Design a solution for securing the administration of cloud tenants, including SaaS and multicloud infrastructure and platforms
- Design a solution for cloud infrastructure entitlement management that includes Microsoft Entra Permissions Management
- Design a solution for Privileged Access Workstation (PAW) and bastion services
Design solutions for regulatory compliance
- Translate compliance requirements into a security solution
- Design a solution to address compliance requirements by using Microsoft Purview risk and compliance solutions
- Design a solution to address privacy requirements, including Microsoft Priva
- Design Azure Policy solutions to address security and compliance requirements
- Evaluate infrastructure compliance by using Microsoft Defender for Cloud
Design solutions for security posture management in hybrid and multicloud environments
- Evaluate security posture by using MCSB
- Evaluate security posture by using Microsoft Defender for Cloud
- Evaluate security posture by using Microsoft Secure Score
- Design integrated security posture management and workload protection solutions in hybrid and multi-cloud environments, including Microsoft Defender for Cloud
- Design cloud workload protection solutions that use Microsoft Defender for Cloud, such as Microsoft Defender for Servers, Microsoft Defender for App Service, and Microsoft Defender for SQL
- Design a solution for integrating hybrid and multicloud environments by using Azure Arc
- Design a solution for Microsoft Defender External Attack Surface Management (Defender EASM)
Design solutions for securing server and client endpoints
- Specify security requirements for servers, including multiple platforms and operating systems
- Specify security requirements for mobile devices and clients, including endpoint protection, hardening, and configuration
- Specify security requirements for IoT devices and embedded systems
- Design a solution for securing operational technology (OT) and industrial control systems (ICS) by using Microsoft Defender for IoT
- Specify security baselines for server and client endpoints
- Design a solution for secure remote access
Specify requirements for securing SaaS, PaaS, and IaaS services
- Specify security baselines for SaaS, PaaS, and IaaS services
- Specify security requirements for IoT workloads
- Specify security requirements for web workloads, including Azure App Service
- Specify security requirements for containers
- Specify security requirements for container orchestration
Design solutions for securing Microsoft 365
- Evaluate security posture for productivity and collaboration workloads by using metrics, including Microsoft Secure Score and Microsoft Defender for Cloud secure score
- Design a Microsoft 365 Defender solution
- Design secure configurations and operational practices for Microsoft 365 workloads and data
Design solutions for securing applications
- Evaluate the security posture of existing application portfolios
- Evaluate threats to business-critical applications by using threat modeling
- Design and implement a full lifecycle strategy for application security
- Design and implement standards and practices for securing the application development process
- Map technologies to application security requirements
- Design a solution for workload identity to authenticate and access Azure cloud resources
- Design a solution for API management and security
- Design a solution for secure access to applications, including Azure Web Application Firewall (WAF) and Azure Front Door
Design solutions for securing an organization’s data
- Design a solution for data discovery and classification by using Microsoft Purview data governance solutions
- Specify priorities for mitigating threats to data
- Design a solution for protection of data at rest, data in motion, and data in use
- Design a security solution for data in Azure workloads, including Azure SQL, Azure Synapse Analytics, and Azure Cosmos DB
- Design a security solution for data in Azure Storage
- Design a security solution that includes Microsoft Defender for Storage and Microsoft Defender for SQL
Course Mode
Instructor-Led Remote Live Classroom Training;
Trainers
Trainers are authorized Instructors in Microsoft and certified in other IT technologies, with years of hands-on experience in the industry and in Training.
Lab Topology
For all types of delivery, the participant can access the equipment and actual systems in our laboratories or directly in international data centers remotely, 24/7. Each participant has access to implement various configurations, Thus immediately applying the theory learned. Below are some scenarios drawn from laboratory activities.
Course Details
Course Prerequisites
Attendance at the Microsoft Security, Compliance, and Identity Fundamentals Course (SC-900) is recommended .
Course Duration
Intensive duration 4 days;
Course Frequency
Course Duration: 4 days (9.00 to 17.00) - Ask for other types of attendance.
Course Date
- Microsoft Cybersecurity Architect Course (Intensive Formula) – On request – 09:00 – 17:00
Steps to Enroll
Registration takes place by asking to be contacted from the following link, or by contacting the office at the international number +355 45 301 313 or by sending a request to the email info@hadartraining.com