Azure Security Technologies AZ-500

The AZ-500 Azure Security Technologies Course is designed for participants interested in a deep understanding of Azure security technologies. Participants will learn to protect data, applications and infrastructure in Azure using advanced security tools. The course covers access management, identity protection, key management, and network security. They will be able to implement security measures, detect and respond to security threats and manage compliance. The course contributes to the preparation of the Azure Security Engineer Associate certification exam .
Course Objectives
Below is a summary of the main objectives of the Azure Security Technologies AZ-500 course :
- Data and application protection in Azure.
- Identity and access management in Azure.
- Implementation of network security.
- Using Azure Key Vault and Azure Sentinel.
- Threat management and regulatory compliance.
- Learn to configure advanced security features, such as Azure Firewall and Azure DDoS Protection, to safeguard Azure environments.
- Understand how to monitor and manage security operations using Azure Monitor and Azure Security Center to detect and respond to security threats in real time.
- Develop expertise in implementing secure application deployment strategies, including the use of Azure DevOps and Azure Blueprints for secure development lifecycle management.
Course Certification
This course helps you prepare to take the:
AZ-500 Microsoft Azure Security Technologies exam
Course Outline
Manage identities in Microsoft Entra ID
- Secure users in Microsoft Entra ID
- Secure groups in Microsoft Entra ID
- Recommend when to use external identities
- Secure external identities
- Implement Microsoft Entra ID Protection
Manage authentication by using Microsoft Entra ID
- Configure Microsoft Entra Verified ID
- Implement multi-factor authentication (MFA)
- Implement passwordless authentication
- Implement password protection
- Implement single sign-on (SSO)
- Integrate single sign on (SSO) and identity providers
- Recommend and enforce modern authentication protocols
Manage authorization by using Microsoft Entra ID
- Configure Azure role permissions for management groups, subscriptions, resource groups, and resources
- Assign built-in roles in Microsoft Entra ID
- Assign built-in roles in Azure
- Create and assign custom roles, including Azure roles and Microsoft Microsoft Entra roles
- Implement and manage Microsoft Entra Permissions Management
- Configure Microsoft Entra Privileged Identity Management (PIM)
- Configure role management and access reviews in Microsoft Entra
- Implement Conditional Access policies
Manage application access in Microsoft Entra ID
- Manage access to enterprise applications in Microsoft Entra ID, including OAuth permission grants
- Manage app registrations in Microsoft Entra ID
- Configure app registration permission scopes
- Manage app registration permission consent
- Manage and use service principals
- Manage managed identities for Azure resources
- Recommend when to use and configure a Microsoft Entra Application Proxy, including authentication
Plan and implement security for virtual networks
- Plan and implement Network Security Groups (NSGs) and Application Security Groups (ASGs)
- Plan and implement user-defined routes (UDRs)
- Plan and implement Virtual Network peering or VPN gateway
- Plan and implement Virtual WAN, including secured virtual hub
- Secure VPN connectivity, including point-to-site and site-to-site
- Implement encryption over ExpressRoute
- Configure firewall settings on PaaS resources
- Monitor network security by using Network Watcher, including NSG flow logging
Plan and implement security for private access to Azure resources
- Plan and implement virtual network Service Endpoints
- Plan and implement Private Endpoints
- Plan and implement Private Link services
- Plan and implement network integration for Azure App Service and Azure Functions
- Plan and implement network security configurations for an App Service Environment (ASE)
- Plan and implement network security configurations for an Azure SQL Managed Instance
Plan and implement security for public access to Azure resources
- Plan and implement Transport Layer Security (TLS) to applications, including Azure App Service and API Management
- Plan, implement, and manage an Azure Firewall, including Azure Firewall Manager and firewall policies
- Plan and implement an Azure Application Gateway
- Plan and implement an Azure Front Door, including Content Delivery Network (CDN)
- Plan and implement a Web Application Firewall (WAF)
- Recommend when to use Azure DDoS Protection Standard
Plan and implement advanced security for compute
- Plan and implement remote access to public endpoints, including Azure Bastion and just-in-time (JIT) virtual machine (VM) access
- Configure network isolation for Azure Kubernetes Service (AKS)
- Secure and monitor AKS
- Configure authentication for AKS
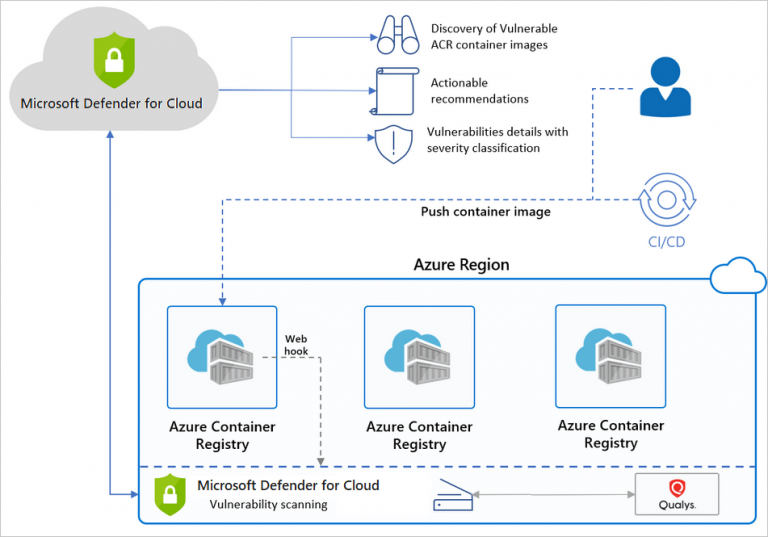
- Configure security monitoring for Azure Container Instances (ACIs)
- Configure security monitoring for Azure Container Apps (ACAs)
- Manage access to Azure Container Registry (ACR)
- Configure disk encryption, including Azure Disk Encryption (ADE), encryption as host, and confidential disk encryption
- Recommend security configurations for Azure API Management
Plan and implement security for storage
- Configure access control for storage accounts
- Manage life cycle for storage account access keys
- Select and configure an appropriate method for access to Azure Files
- Select and configure an appropriate method for access to Azure Blob Storage
- Select and configure an appropriate method for access to Azure Tables
- Select and configure an appropriate method for access to Azure Queues
- Select and configure appropriate methods for protecting against data security threats, including soft delete, backups, versioning, and immutable storage
- Configure Bring your own key (BYOK)
- Enable double encryption at the Azure Storage infrastructure level
Plan and implement security for Azure SQL Database and Azure SQL Managed Instance
- Enable database authentication by using Microsoft Entra ID
- Enable database auditing
- Identify use cases for the Microsoft Purview governance portal
- Implement data classification of sensitive information by using the Microsoft Purview governance portal
- Plan and implement dynamic masking
- Implement Transparent Database Encryption (TDE)
- Recommend when to use Azure SQL Database Always Encrypted
Plan, implement, and manage governance for security
- Create, assign, and interpret security policies and initiatives in Azure Policy
- Configure security settings by using Azure Blueprint
- Deploy secure infrastructures by using a landing zone
- Create and configure an Azure Key Vault
- Recommend when to use a dedicated Hardware Security Module (HSM)
- Configure access to Key Vault, including vault access policies and Azure Role Based Access Control
- Manage certificates, secrets, and keys
- Configure key rotation
- Configure backup and recovery of certificates, secrets, and keys
Manage security posture by using Microsoft Defender for Cloud
- Identify and remediate security risks by using the Microsoft Defender for Cloud Secure Score and Inventory
- Assess compliance against security frameworks and Microsoft Defender for Cloud
- Add industry and regulatory standards to Microsoft Defender for Cloud
- Add custom initiatives to Microsoft Defender for Cloud
- Connect hybrid cloud and multi-cloud environments to Microsoft Defender for Cloud
- Identify and monitor external assets by using Microsoft Defender External Attack Surface Management
Configure and manage threat protection by using Microsoft Defender for Cloud
- Enable workload protection services in Microsoft Defender for Cloud, including Microsoft Defender for Storage, Databases, Containers, App Service, Key Vault, Resource Manager, and DNS
- Configure Microsoft Defender for Servers
- Configure Microsoft Defender for Azure SQL Database
- Manage and respond to security alerts in Microsoft Defender for Cloud
- Configure workflow automation by using Microsoft Defender for Cloud
- Evaluate vulnerability scans from Microsoft Defender for Server
Configure and manage security monitoring and automation solutions
- Monitor security events by using Azure Monitor
- Configure data connectors in Microsoft Sentinel
- Create and customize analytics rules in Microsoft Sentinel
- Evaluate alerts and incidents in Microsoft Sentinel
- Configure automation in Microsoft Sentinel
Course Mode
Instructor-Led Remote Live Classroom Training;
Trainers
Trainers are authorized Instructors in Microsoft and certified in other IT technologies, with years of hands-on experience in the industry and in Training.
Lab Topology
For all types of delivery, the participant can access the equipment and actual systems in our laboratories or directly in international data centers remotely, 24/7. Each participant has access to implement various configurations, Thus immediately applying the theory learned. Below are some scenarios drawn from laboratory activities.
Course Details
Course Prerequisites
Participation in the Azure Administrator course is recommended .
Course Duration
Intensive duration 4 days;
Course Frequency
Course Duration: 4 days (9.00 to 17.00) - Ask for other types of attendance.
Course Date
- Azure Security Technologies Course (Intensive Formula) – On request – 09:00 – 17:00
Steps to Enroll
Registration takes place by asking to be contacted from the following link, or by contacting the office at the international number +355 45 301 313 or by sending a request to the email info@hadartraining.com